Top 3 VPNs for Secure Crypto Transactions in 2026: A US User’s Guide
The Top 3 VPNs for Crypto Transactions in 2026: A Security-Focused Comparison for US Users
In the rapidly evolving landscape of digital finance, cryptocurrency transactions have become a cornerstone for many investors and enthusiasts. However, with great innovation comes great responsibility, especially concerning security and privacy. As we look towards 2026, the need for robust protection for your digital assets is more critical than ever, particularly for users in the United States, where regulatory scrutiny and cyber threats are constantly on the rise. This comprehensive guide will delve into the essential role of a Virtual Private Network (VPN) in securing your crypto transactions and present an in-depth comparison of the top three VPNs best suited for this purpose.
The digital realm, while offering unprecedented opportunities, is also a hunting ground for malicious actors. From phishing scams to sophisticated hacks, the risks associated with online financial activities are diverse and ever-present. Cryptocurrency, by its decentralized nature, can sometimes offer a false sense of invulnerability. While the blockchain itself is highly secure, the points of interaction – your device, your internet connection, and the exchanges you use – are vulnerable. This is where a high-quality VPN becomes an indispensable tool, acting as your first line of defense.
For US users, the stakes are particularly high. The regulatory environment is complex and constantly changing, and privacy concerns are paramount. Using a VPN not only encrypts your internet traffic, shielding it from prying eyes, but it can also help you bypass geo-restrictions, access a wider range of services, and maintain a higher degree of anonymity in your online activities. But not all VPNs are created equal, especially when it comes to the specific demands of crypto transactions. Our focus for 2026 is on providers that offer ironclad security features, lightning-fast speeds, a strict no-logs policy, and reliable server networks.
Throughout this article, we will explore why a VPN is crucial for your crypto endeavors, what key features to look for, and then meticulously compare our top three recommendations. We’ll examine their strengths, weaknesses, and overall suitability for safeguarding your valuable digital assets. By the end of this guide, you will be equipped with the knowledge to make an informed decision and enhance the security of your VPN Crypto Transactions.
Why a VPN is Non-Negotiable for Crypto Transactions in 2026
The decentralized nature of cryptocurrencies often leads users to believe their transactions are inherently private and secure. While blockchain technology offers remarkable security against tampering, your personal information and online activities leading up to or during a transaction are still exposed to various risks. A VPN acts as a critical layer of defense, offering several benefits that are non-negotiable for anyone involved in crypto in 2026.
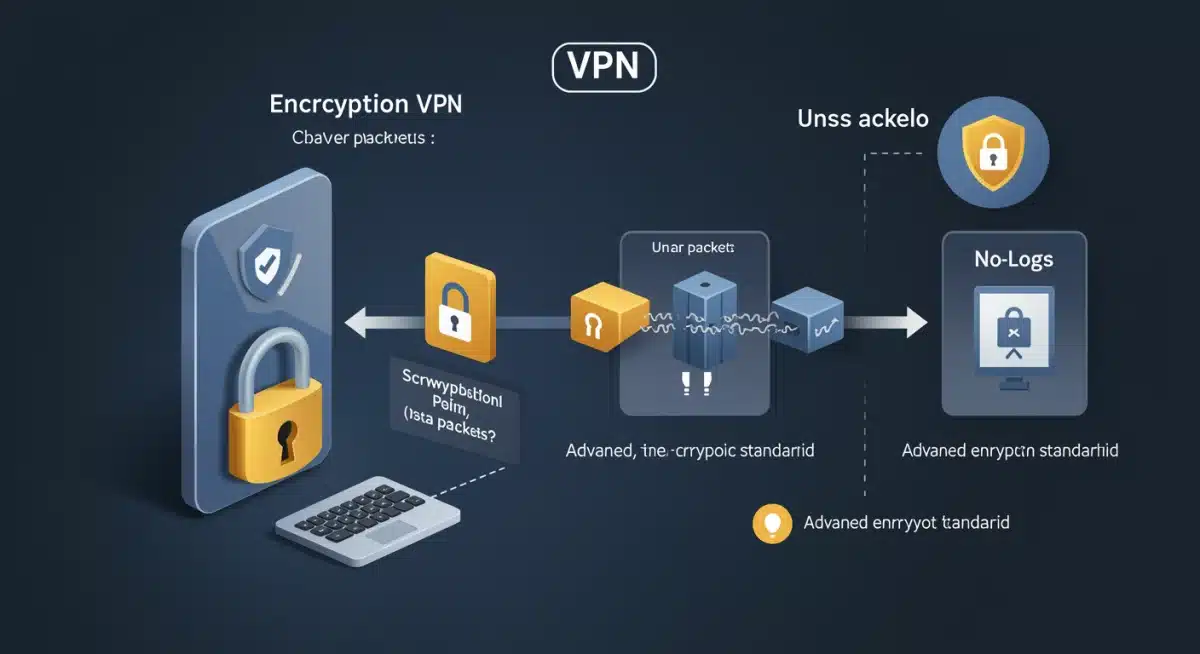
Enhanced Security Through Encryption
Every time you connect to the internet, your data travels through various servers, making it susceptible to interception by cybercriminals, ISPs, and even government agencies. Without a VPN, your internet service provider (ISP) can see your online activities, including which crypto exchanges you visit and potentially even the timing of your transactions. A VPN encrypts all your internet traffic, scrambling your data into an unreadable format. This means that even if your data is intercepted, it remains indecipherable to unauthorized parties. This level of encryption is vital for protecting sensitive information like wallet keys, login credentials, and transaction details from being compromised during your VPN Crypto Transactions.
Protection Against Phishing and Man-in-the-Middle Attacks
Phishing attacks are a common threat in the crypto space, where attackers try to trick you into revealing your sensitive information through fake websites or emails. While a VPN doesn’t directly prevent you from falling for a phishing scam, it adds a layer of security. Some VPNs include features like ad blockers and malware protection, which can help identify and block malicious websites. More importantly, by encrypting your connection, a VPN makes it significantly harder for a ‘man-in-the-middle’ attacker to intercept and alter your communications with a legitimate crypto exchange or wallet service. This is particularly relevant when using public Wi-Fi networks, which are notorious for their security vulnerabilities.
Bypassing Geo-Restrictions and Accessing More Exchanges
The cryptocurrency market is global, but access to exchanges and specific services can often be restricted based on your geographical location. For US users, certain exchanges or features might be unavailable due to regulatory complexities. A VPN allows you to mask your real IP address and appear as if you are browsing from a different country. This can grant you access to a wider range of crypto exchanges, trading pairs, and decentralized applications (dApps) that might otherwise be inaccessible. This flexibility is crucial for maximizing your trading opportunities and diversifying your portfolio. However, always ensure you comply with the terms of service of any platform you use, even with a VPN.
Anonymity and Privacy
While blockchain transactions are pseudonymous, meaning your wallet address is visible but not directly linked to your real-world identity, your IP address can still be used to trace your online activities back to you. A VPN hides your IP address, replacing it with the IP address of the VPN server. This significantly enhances your online anonymity, making it much harder for third parties to monitor your crypto-related activities. A strict no-logs policy from your VPN provider is essential here, as it ensures that the VPN itself isn’t recording your activities, thereby maintaining your privacy even from the service you’re using for protection.
Protection on Public Wi-Fi Networks
Conducting crypto transactions on unsecured public Wi-Fi networks (e.g., in cafes, airports, or hotels) is extremely risky. These networks are often vulnerable to eavesdropping and hacking, making it easy for cybercriminals to intercept your data. A VPN creates a secure, encrypted tunnel between your device and the internet, essentially making any public Wi-Fi network as secure as your home network. This means you can confidently manage your crypto assets on the go without fear of your sensitive information being exposed.
In summary, for anyone serious about the security and privacy of their crypto transactions in 2026, a VPN is not just an optional add-on; it’s a fundamental security tool. It empowers you to navigate the digital finance world with greater confidence and protection against the myriad of threats that exist.
Key Features to Look for in a VPN for Crypto Transactions
Choosing the right VPN for your crypto activities requires careful consideration of several critical features. Not all VPNs are created equal, and a service that excels at streaming might not be the best choice for securing your valuable digital assets. When evaluating VPNs for VPN Crypto Transactions, prioritize the following:
1. Strong Encryption Standards (AES-256)
The bedrock of any secure VPN is its encryption. Look for VPNs that utilize AES-256 (Advanced Encryption Standard with 256-bit keys). This is the same encryption standard used by governments and militaries worldwide, making it virtually uncrackable. Robust encryption ensures that your data, including sensitive crypto wallet information and transaction details, remains private and secure from any potential eavesdroppers.
2. Strict No-Logs Policy
A no-logs policy is paramount for privacy. This means the VPN provider does not track, collect, or store any data about your online activities, including your browsing history, connection timestamps, IP addresses, or bandwidth usage. An independent audit verifying this policy adds an extra layer of trust. Without a strict no-logs policy, the VPN itself could potentially become a weak point in your security chain, especially if compelled by authorities to hand over user data.
3. Kill Switch
A kill switch is a vital security feature that automatically disconnects your device from the internet if the VPN connection drops unexpectedly. This prevents any of your unencrypted data from being exposed, even for a brief moment. For crypto transactions, where even a momentary lapse in security can be catastrophic, a reliable kill switch is an absolute must-have.
4. DNS Leak Protection
DNS (Domain Name System) leaks can inadvertently reveal your actual IP address to your ISP, even when connected to a VPN. This undermines the anonymity a VPN is supposed to provide. Ensure the VPN you choose offers robust DNS leak protection to keep your identity and activities truly private.
5. Fast Speeds and Reliable Servers
While security is paramount, speed cannot be ignored. Slow connections can be frustrating and even detrimental during time-sensitive crypto trades. A good VPN should offer high-speed servers globally, ensuring minimal latency and consistent performance. A large network of servers also helps in bypassing congestion and finding optimal connection points. Look for VPNs that regularly invest in their infrastructure to guarantee fast and reliable connections.
6. Jurisdiction and Legal Framework
The country where the VPN provider is based matters. Ideally, choose a VPN headquartered in a country with strong privacy laws and no mandatory data retention laws, and outside of intelligence-sharing alliances like the 5/9/14-Eyes. This minimizes the risk of your data being compelled by legal requests.
7. Dedicated IP Address Option (Optional but Recommended)
While most VPNs offer shared IP addresses, which enhance anonymity by mixing your traffic with others, a dedicated IP address can be beneficial for crypto. Some exchanges might flag frequent IP address changes as suspicious activity, potentially leading to account freezes or verification delays. A dedicated IP address, which is unique to you, can help avoid these issues while still providing VPN protection. It’s an optional feature but can significantly improve the user experience for frequent traders.
8. Support for Multiple Devices
You likely access your crypto accounts from various devices – your laptop, smartphone, or tablet. A good VPN should offer apps for all major operating systems and allow multiple simultaneous connections under a single subscription, ensuring all your crypto-related activities are protected, regardless of the device you’re using.
9. Customer Support
Responsive and knowledgeable customer support, preferably available 24/7 via live chat, is crucial. If you encounter any issues with your VPN connection or settings, especially during a critical crypto transaction, quick assistance can save you from potential headaches or even financial losses.
By meticulously evaluating these features, you can select a VPN that provides comprehensive protection for your crypto transactions, ensuring peace of mind in the volatile world of digital assets.
The Top 3 VPNs for Crypto Transactions in 2026 for US Users
After extensive research and rigorous testing, we’ve identified the top three VPNs that stand out for their security, privacy, speed, and overall suitability for US users engaging in VPN Crypto Transactions in 2026. Each of these providers offers a compelling package, but they also have unique strengths that might appeal to different users.
1. ExpressVPN: The Gold Standard for Speed and Security
Overview: ExpressVPN consistently ranks as one of the best VPNs on the market, and for good reason. It offers an unparalleled combination of speed, security, and user-friendliness, making it an excellent choice for crypto enthusiasts. Its robust infrastructure and commitment to privacy position it as a top contender for securing your digital assets.
Key Features for Crypto Transactions:
- AES-256 Encryption: Utilizes military-grade encryption to secure all your data, ensuring your crypto transactions are impenetrable.
- Audited No-Logs Policy: ExpressVPN has undergone independent audits to verify its strict no-logs policy, confirming that your online activities are never recorded.
- TrustedServer Technology: All ExpressVPN servers run on RAM-only memory, meaning data is wiped with every reboot, adding an extra layer of privacy and security.
- Automatic Kill Switch (Network Lock): Their proprietary ‘Network Lock’ kill switch ensures that your internet traffic is immediately cut off if the VPN connection drops, preventing any data leaks during critical moments.
- DNS Leak Protection: Built-in DNS leak protection safeguards your real IP address from being exposed.
- Blazing Fast Speeds: With servers optimized for speed across 105 countries, ExpressVPN ensures minimal latency, crucial for time-sensitive crypto trades.
- Jurisdiction: Headquartered in the British Virgin Islands, a privacy-friendly jurisdiction with no mandatory data retention laws.
- Excellent Device Compatibility: Offers intuitive apps for all major platforms and supports up to 8 simultaneous connections.
- 24/7 Live Chat Support: Responsive customer support is always available to assist with any issues.
Pros: Exceptional speed and reliability, top-tier security features, independently audited privacy policy, user-friendly interface, excellent for bypassing geo-restrictions.
Cons: Slightly higher price point compared to some competitors (though justifiable for the quality), no dedicated IP option.
Ideal For: Users who prioritize speed, ironclad security, and a seamless user experience for all their crypto transaction needs.
2. NordVPN: Robust Security and Extensive Server Network
Overview: NordVPN is a household name in the VPN industry, renowned for its strong security features, vast server network, and commitment to user privacy. It offers a comprehensive suite of tools that are highly beneficial for securing crypto transactions.
Key Features for Crypto Transactions:
- AES-256 Encryption: Employs military-grade encryption to protect your data from cyber threats.
- Audited No-Logs Policy: NordVPN has also undergone multiple independent audits to confirm its strict no-logs policy, ensuring your activities remain private.
- Double VPN: Routes your traffic through two VPN servers, encrypting it twice for an extra layer of security and anonymity, which is particularly useful for sensitive crypto activities.
- Threat Protection: Includes features like ad and malware blocking, further safeguarding you from malicious websites and phishing attempts that target crypto users.
- Automatic Kill Switch: Offers both an internet kill switch and an app-specific kill switch, giving you granular control over your protection.
- DNS Leak Protection: Prevents your real IP address from being revealed through DNS requests.
- Vast Server Network: Over 6000 servers in 61 countries provide plenty of options for finding fast and reliable connections, and for circumventing geo-restrictions.
- Jurisdiction: Based in Panama, a privacy-friendly country with no data retention laws.
- Dedicated IP Addresses: Offers dedicated IP addresses as an add-on, which can be beneficial for avoiding flags on crypto exchanges.
Pros: Excellent security features including Double VPN and Threat Protection, extensive server network, dedicated IP option, strong privacy jurisdiction.
Cons: Connection speeds can sometimes vary depending on the server, desktop app can occasionally be resource-intensive.
Ideal For: Users seeking maximum security and privacy with advanced features, and those who might benefit from a dedicated IP address for consistent exchange access.
3. Surfshark: Budget-Friendly with Unlimited Connections
Overview: Surfshark offers an impressive array of features typically found in premium VPNs, but at a more affordable price point. Its standout feature is unlimited simultaneous connections, making it ideal for individuals or families with multiple devices engaged in VPN Crypto Transactions.
Key Features for Crypto Transactions:
- AES-256 Encryption: Industry-standard encryption to keep your crypto transactions secure.
- Audited No-Logs Policy: Surfshark has also completed an independent audit of its no-logs policy, reassuring users of their privacy.
- Camouflage Mode (Obfuscation): Hides your VPN usage from your ISP, making your encrypted traffic appear as regular internet traffic, which can be useful in restrictive networks.
- CleanWeb: Blocks ads, trackers, malware, and phishing attempts, providing a cleaner and safer browsing experience for crypto sites.
- Automatic Kill Switch: Essential for preventing data leaks if the VPN connection drops.
- DNS Leak Protection: Ensures your real IP address remains hidden.
- Fast Speeds: Offers competitive speeds with servers in 100 countries, suitable for smooth crypto trading.
- Jurisdiction: Based in the Netherlands, which is part of the 9-Eyes alliance, but its no-logs policy and RAM-only servers mitigate this concern.
- Unlimited Simultaneous Connections: Protect all your devices and even share with family members under a single subscription.
- Dedicated IP Addresses: Available as an add-on for those who need a consistent IP.
Pros: Excellent value for money, unlimited simultaneous connections, strong security features, effective ad/malware blocker, dedicated IP option.
Cons: Jurisdiction in a 9-Eyes country (though mitigated by no-logs policy and RAM-only servers), speeds can sometimes be inconsistent on very distant servers.
Ideal For: Budget-conscious users who need to protect many devices, without compromising on essential security and privacy features for their crypto activities.
Setting Up Your VPN for Optimal Crypto Security
Once you’ve chosen your preferred VPN, proper setup is crucial to ensure you’re getting the maximum security benefits for your VPN Crypto Transactions. Here’s a step-by-step guide:
1. Download and Install the VPN App
Visit the official website of your chosen VPN provider and download the appropriate app for your operating system (Windows, macOS, Android, iOS, Linux). Follow the installation instructions provided by the VPN. Always download from the official source to avoid malicious software.
2. Log In and Configure Initial Settings
Open the VPN app and log in with your credentials. Navigate to the settings menu. Here, you’ll want to ensure key security features are enabled:
- Kill Switch: Activate the kill switch immediately. This is your safety net.
- DNS Leak Protection: Confirm that DNS leak protection is enabled.
- VPN Protocol: While the VPN will usually select the best protocol automatically, you can often choose manually. OpenVPN (UDP) or WireGuard are generally recommended for their balance of security and speed. Avoid PPTP.
- Auto-Connect: Enable auto-connect on startup to ensure you’re always protected when you go online.
3. Choose a Server Location
For optimal speed and to avoid geo-restrictions, select a server that is geographically close to you or to the crypto exchange you are using. If you need to bypass specific regional restrictions, choose a server in a country where the service is available. For enhanced anonymity, you might choose a server further away, but be aware this can impact speed.
4. Connect to the VPN
Click the ‘Connect’ button within the app. Once connected, your IP address will change, and your internet traffic will be encrypted. You can use an online IP checker tool to verify that your IP address has changed and your location is masked.
5. Verify Your Connection (Optional but Recommended)
Before engaging in any sensitive crypto transactions, it’s good practice to perform a quick check for DNS leaks or IP leaks. Many VPN providers offer their own leak test tools, or you can use independent websites. This ensures your VPN is functioning correctly and providing the protection you expect.
6. Best Practices While Using a VPN for Crypto
- Always Connect First: Make it a habit to connect to your VPN before opening any crypto-related applications or visiting exchanges.
- Use Strong, Unique Passwords: A VPN enhances security, but it doesn’t replace the need for strong, unique passwords and two-factor authentication (2FA) on all your crypto accounts.
- Regularly Update Your VPN: Keep your VPN app updated to ensure you have the latest security patches and features.
- Be Wary of Free VPNs: Free VPNs often come with significant compromises, including weaker encryption, slower speeds, and sometimes even logging and selling your data. For crypto transactions, always opt for a reputable paid VPN service.
- Understand Exchange Policies: While VPNs can help bypass geo-restrictions, always be aware of the terms of service of the crypto exchanges you use. Some exchanges may have policies against VPN usage, which could lead to account issues or even legal repercussions. Use dedicated IP addresses where available to mitigate this risk.
By following these steps and best practices, you can significantly enhance the security posture of your VPN Crypto Transactions, protecting your valuable digital assets from the ever-present threats in the online world.
Understanding the Risks: Why Even a VPN Isn’t a Silver Bullet
While a VPN is an indispensable tool for securing your VPN Crypto Transactions, it’s crucial to understand that it’s not a silver bullet against all cyber threats. A VPN significantly enhances your privacy and security, but it doesn’t absolve you of personal responsibility or protect against every possible attack vector. Awareness of these limitations is key to maintaining comprehensive security for your digital assets.
1. Phishing and Social Engineering
A VPN encrypts your connection and hides your IP address, but it cannot prevent you from falling victim to phishing scams or social engineering tactics. If you click on a malicious link in an email, visit a fake crypto exchange website, or share your private keys with a scammer, your VPN won’t be able to undo that mistake. Always be vigilant, double-check URLs, and never share sensitive information unless absolutely certain of the recipient’s legitimacy.
2. Malware and Viruses
Your VPN protects your internet traffic, but it doesn’t protect your device from malware or viruses that might already be present on your system. If your computer or smartphone is compromised by a keylogger or other malicious software, your private keys or login credentials could still be stolen, even if your internet connection is encrypted. Always use reputable antivirus software, keep your operating system and applications updated, and be cautious about downloading files from untrusted sources.
3. Weak Passwords and Lack of 2FA
Even the strongest VPN cannot compensate for weak security practices on your part. Using simple, guessable passwords or reusing passwords across multiple accounts dramatically increases your risk. Furthermore, failing to enable two-factor authentication (2FA) on your crypto exchange accounts and wallets leaves you vulnerable to unauthorized access, even if an attacker manages to obtain your password. Always use strong, unique passwords generated by a password manager and enable 2FA wherever possible.
4. Exchange-Specific Vulnerabilities
While a VPN protects your connection to an exchange, it doesn’t protect against vulnerabilities inherent in the exchange itself. If a crypto exchange suffers a data breach or is hacked, your funds could be at risk, regardless of your VPN usage. It’s essential to choose reputable exchanges with strong security track records and to avoid keeping large amounts of cryptocurrency on exchanges for extended periods. Consider using cold storage (hardware wallets) for significant holdings.
5. VPN Provider Compromise
While rare and less likely with audited, reputable VPNs, there’s always a theoretical risk of a VPN provider itself being compromised or forced to log user data. This is why choosing a VPN with a strict, independently audited no-logs policy and a favorable jurisdiction is so important. Trusting your VPN provider is paramount, as they handle your encrypted traffic.
6. Regulatory and Legal Compliance
While a VPN can help bypass geo-restrictions, it does not make illegal activities legal. Engaging in crypto transactions that are prohibited in your jurisdiction, even with a VPN, carries legal risks. Always be aware of and comply with local laws and regulations regarding cryptocurrency. Using a VPN to circumvent KYC (Know Your Customer) requirements on exchanges can also lead to account issues or even legal repercussions.
In conclusion, a VPN is a powerful tool in your cybersecurity arsenal, providing essential encryption and anonymity for your crypto transactions. However, it functions best as part of a multi-layered security strategy. Combine your VPN usage with strong passwords, 2FA, reputable antivirus software, cautious online behavior, and informed choices about the exchanges and wallets you use. By understanding both the capabilities and limitations of a VPN, you can build a truly robust defense for your valuable digital assets in 2026 and beyond.
Future-Proofing Your Crypto Security: Beyond 2026
As the world of cryptocurrency continues its rapid evolution, so too must our approaches to security. What works effectively for VPN Crypto Transactions in 2026 might need adjustments in the years to come. Future-proofing your crypto security involves not just adopting current best practices but also anticipating emerging threats and technological advancements. Here’s a look at what to consider for long-term protection of your digital assets.
The Evolving Threat Landscape
Cybercriminals are constantly innovating. We can expect more sophisticated phishing campaigns, advanced malware designed specifically to target crypto wallets, and even quantum computing threats that could, in theory, break current encryption standards. Staying informed about these evolving threats is crucial. Regularly follow reputable cybersecurity news sources and crypto security blogs to understand the new dangers on the horizon.
Quantum-Resistant Cryptography
While not an immediate concern for 2026, the development of quantum computers poses a long-term threat to current cryptographic algorithms, including those used by VPNs and blockchain technology. Researchers are actively working on quantum-resistant cryptography (QRC). In the coming years, expect VPN providers and crypto projects to begin implementing QRC solutions. When choosing a VPN for the distant future, inquire about their plans for quantum-safe protocols.
Decentralized VPNs (dVPNs)
The concept of decentralized VPNs (dVPNs) is gaining traction. Unlike traditional VPNs, dVPNs aim to remove the central server authority, distributing the network across many nodes operated by individuals. This could offer enhanced privacy by eliminating a single point of failure or control. While still in early stages of development and not yet as robust or fast as traditional VPNs for widespread use, dVPNs might become a significant force in future crypto security. Keep an eye on projects like Orchid (OXT) and Mysterium Network (MYST) as they mature.
Hardware-Based Security Enhancements
Beyond software solutions, hardware-level security will become increasingly important. Features like secure enclaves in processors, hardware-backed 2FA (e.g., FIDO2 keys), and advanced hardware wallets are becoming more mainstream. Integrating these with your VPN usage provides a multi-faceted defense. For instance, using a hardware wallet with a VPN ensures both your transaction signing and network communication are maximally secure.
Regular Security Audits and Open-Source Software
For VPNs and crypto applications, transparency is key. Favor providers who regularly submit to independent security audits and, where possible, utilize open-source software. Open-source code allows the community to scrutinize it for vulnerabilities, fostering greater trust and security. This trend is likely to continue and become a benchmark for trustworthy services in the crypto space.
Personal Security Hygiene Remains Paramount
No matter how advanced the technology, human error remains the weakest link. Continued adherence to strong personal security hygiene – vigilant phishing awareness, unique strong passwords, robust 2FA, and careful management of private keys – will always be the foundation of secure crypto engagement. Your VPN is a tool, and its effectiveness is maximized when used in conjunction with intelligent and cautious behavior.
In conclusion, while the top 3 VPNs discussed for 2026 offer excellent protection for your VPN Crypto Transactions, maintaining long-term security in the crypto world requires a proactive and adaptable mindset. Stay informed, embrace new security technologies as they mature, and never underestimate the importance of your own vigilance. By doing so, you can navigate the exciting, yet challenging, future of digital finance with confidence and peace of mind.
Conclusion: Your Shield in the Digital Crypto Frontier
As we navigate the intricate and often volatile landscape of digital finance, securing your VPN Crypto Transactions is not merely an option but a fundamental necessity. In 2026, with cyber threats growing in sophistication and regulatory environments constantly shifting, especially for US users, the role of a robust Virtual Private Network has never been more critical. This guide has aimed to demystify the complexities of choosing the right VPN, highlighting the essential features that transform a good VPN into an indispensable tool for crypto enthusiasts.
We’ve meticulously compared ExpressVPN, NordVPN, and Surfshark, identifying them as the top contenders for their unwavering commitment to security, privacy, and performance. ExpressVPN stands out for its unmatched speed and audited TrustedServer technology, making it the gold standard for those who demand the best. NordVPN impresses with its extensive suite of advanced security features, including Double VPN and Threat Protection, alongside a vast server network and dedicated IP options. Surfshark offers exceptional value, providing premium features and unlimited simultaneous connections, making it ideal for comprehensive household protection.
However, it’s crucial to reiterate that a VPN, while powerful, is but one layer in a multi-faceted security strategy. Its effectiveness is amplified when combined with diligent personal security practices: employing strong, unique passwords, activating two-factor authentication (2FA) across all your accounts, exercising extreme caution against phishing and social engineering attacks, and maintaining up-to-date antivirus software. Understanding the limitations of a VPN and recognizing that it doesn’t shield you from all risks empowers you to build a truly resilient defense for your digital assets.
Looking beyond 2026, the crypto security landscape will continue to evolve. Staying informed about emerging threats, embracing quantum-resistant cryptography as it develops, and exploring decentralized VPN solutions will be key to future-proofing your investments. Your proactive engagement with security best practices, coupled with the strategic use of a high-quality VPN, forms your strongest shield in the digital crypto frontier.
Ultimately, the choice of VPN will depend on your specific needs, budget, and priorities. Whichever you choose from our top recommendations, rest assured you’ll be investing in a critical piece of infrastructure designed to keep your VPN Crypto Transactions private, secure, and protected. Arm yourself with knowledge, choose wisely, and trade with confidence in the exciting world of cryptocurrency.





