Crypto Hacks 2025: Forensic Analysis for 2026 US Security

The forensic analysis of major crypto hacks in 2025 reveals critical vulnerabilities and sophisticated attack vectors that demand immediate attention to fortify US digital security infrastructure in 2026.
The digital frontier is constantly under siege, and the cryptocurrency landscape, in particular, has become a prime target for sophisticated cybercriminals. Understanding the intricacies of these attacks is paramount for safeguarding digital assets and national security. This article delves into a comprehensive forensic analysis of crypto hacks from 2025, extracting crucial lessons that will shape US digital security strategies in 2026.
The evolving threat landscape in 2025
The year 2025 witnessed an alarming escalation in the frequency and sophistication of crypto-related cyberattacks. Threat actors, ranging from individual hackers to state-sponsored groups, leveraged novel techniques to exploit vulnerabilities across various blockchain platforms and decentralized finance (DeFi) protocols. This shift necessitates a deeper understanding of their methodologies to build resilient defenses.
New attack vectors and vulnerabilities
Attackers in 2025 moved beyond simple phishing scams, increasingly targeting complex smart contract logic and cross-chain bridge mechanisms. Supply chain attacks on crypto infrastructure also became more prevalent, compromising trusted software components. These new vectors highlight a critical need for continuous security auditing and real-time threat intelligence sharing.
- Sophisticated smart contract exploits manipulating token balances.
- Cross-chain bridge vulnerabilities leading to significant asset drains.
- Supply chain compromises affecting widely used crypto development tools.
- Social engineering tactics targeting high-value individuals within crypto projects.
The sheer diversity of these attack methods underscores that a multi-layered security approach is no longer optional but a fundamental requirement. Organizations must anticipate and mitigate risks from various angles, from code-level vulnerabilities to human factors.
Key forensic techniques implemented
Responding to the surge in incidents, forensic analysts in 2025 refined their methodologies to trace stolen funds, identify perpetrators, and understand attack patterns. These techniques are vital for both recovery efforts and preventative measures, providing invaluable insights into the anatomy of a hack.
On-chain analysis and tracing
Tracing illicit funds on public blockchains involves meticulous analysis of transaction flows, often spanning multiple chains and mixer services. Advanced analytics tools and AI-driven algorithms played a significant role in de-anonymizing transactions and identifying suspicious activity. The challenge lies in navigating increasingly sophisticated obfuscation techniques employed by attackers.
Investigators employed specialized software to follow the movement of stolen cryptocurrencies, even when they passed through decentralized exchanges or privacy coins. This process often required collaboration with various blockchain analytics firms and international law enforcement agencies to achieve success. The transparency of blockchain, while a double-edged sword, ultimately aids in forensic investigations.
Off-chain intelligence gathering
Beyond the blockchain, forensic efforts extended to traditional cybersecurity investigations, including analyzing compromised servers, phishing infrastructure, and communication channels used by attackers. This off-chain intelligence often provided critical links to real-world identities and criminal networks, bridging the gap between digital footprints and actionable intelligence.
- Analysis of server logs and network traffic for intrusion detection.
- Examination of phishing emails and campaign infrastructure.
- Social media monitoring and dark web intelligence to identify threat actors.
- Collaboration with ISPs and hosting providers to take down malicious infrastructure.
The integration of on-chain and off-chain data proved essential for painting a complete picture of the attack, allowing for more effective attribution and recovery strategies. This holistic approach is becoming the standard for complex crypto investigations.
Notable crypto incidents of 2025 and their impact
Several high-profile crypto hacks in 2025 served as stark reminders of the industry’s vulnerabilities, collectively resulting in billions of dollars in losses. Each incident provided unique lessons, exposing new attack vectors and highlighting systemic weaknesses within the ecosystem.
Major DeFi protocol compromises
DeFi protocols, with their intricate smart contract interactions and pooled liquidity, remained a primary target. Flash loan attacks, re-entrancy vulnerabilities, and oracle manipulation exploits continued to dominate the landscape. These incidents often led to massive liquidity drains, impacting thousands of users and shaking investor confidence.
One notable incident involved a major lending protocol that was exploited due to a subtle re-entrancy bug in its smart contract. Attackers repeatedly withdrew funds before the balance was updated, siphoning off hundreds of millions. This highlighted the critical need for independent, multi-auditor reviews of all smart contract code before deployment.
Cross-chain bridge breaches
The increasing interconnectedness of blockchain networks through cross-chain bridges also presented new attack surfaces. Several significant breaches occurred where vulnerabilities in bridge contracts allowed attackers to mint unauthorized tokens on one chain or drain assets locked on another. These incidents underscored the inherent risks of interoperability solutions.
- Exploitation of signature verification mechanisms in bridge protocols.
- Compromise of bridge operator keys leading to unauthorized transactions.
- Logical flaws in token wrapping and unwrapping processes across chains.
The forensic analysis of these bridge attacks revealed a pattern of sophisticated social engineering combined with technical exploits, often targeting the operational security of the bridge maintainers. Strengthening these critical infrastructure points is paramount for the future of multi-chain ecosystems.
Lessons learned for US security in 2026
The incidents of 2025 provided invaluable, albeit costly, lessons that are directly applicable to strengthening US digital security infrastructure in 2026. These insights transcend the crypto space, offering broader implications for critical infrastructure protection and national cybersecurity.
Enhanced regulatory frameworks
The lack of consistent regulatory oversight across the crypto industry proved to be a significant weakness. In 2026, there is a clear push for more robust, yet adaptable, regulatory frameworks that encourage innovation while mandating higher security standards. This includes clearer guidelines for DeFi protocols, stablecoins, and centralized exchanges operating within US jurisdiction.
Policymakers are exploring ways to implement regulations that address issues like KYC (Know Your Customer) and AML (Anti-Money Laundering) more effectively in decentralized contexts, without stifling technological advancement. The goal is to create a safer environment for users and legitimate businesses while deterring illicit activities.
Investing in forensic capabilities and threat intelligence
The ability to rapidly respond to and forensically analyze crypto hacks is crucial. This necessitates significant investment in advanced forensic tools, training for law enforcement and cybersecurity professionals, and fostering stronger public-private partnerships for threat intelligence sharing. Real-time data feeds on emerging attack patterns and vulnerabilities are essential.
- Development of AI-powered anomaly detection systems for blockchain transactions.
- Cross-agency training programs focused on crypto-specific forensic techniques.
- Establishment of a national threat intelligence sharing platform for crypto incidents.
By prioritizing these investments, the US can significantly reduce the time required to detect, analyze, and mitigate cyber threats in the crypto domain, enhancing overall national security.
Proactive security measures for 2026
Moving beyond reactive responses, 2026 demands a proactive stance on digital security, especially concerning the burgeoning Web3 ecosystem. This involves implementing preventative strategies that anticipate potential threats rather than merely reacting to them.
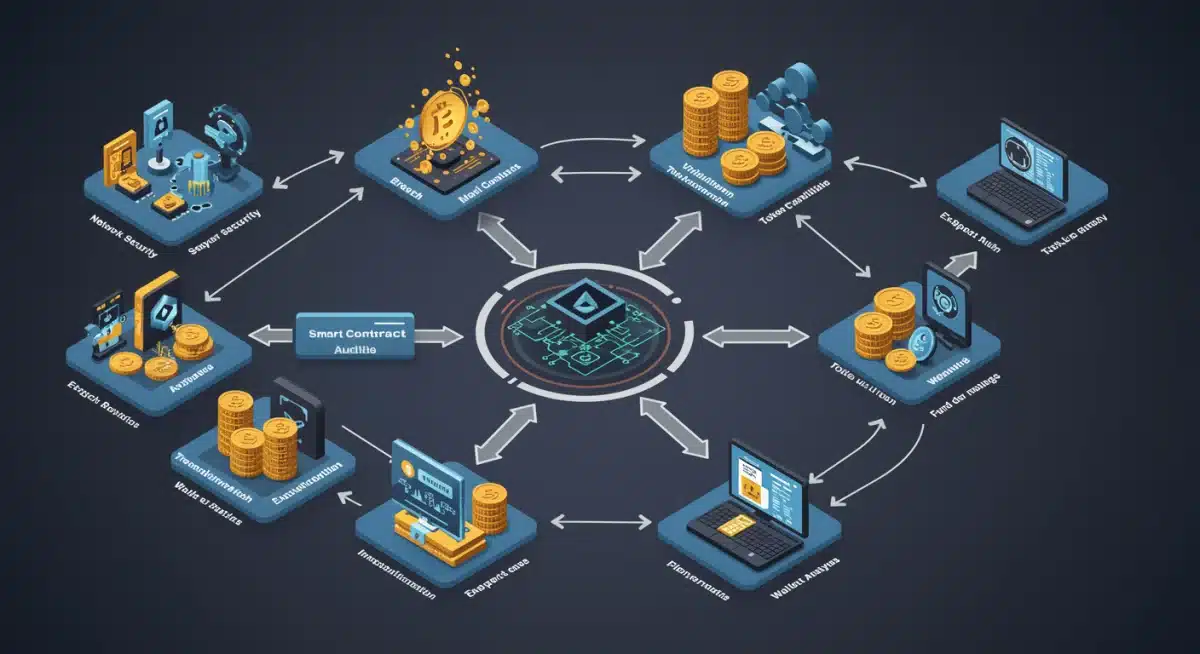
Strengthening smart contract auditing and formal verification
The pervasive nature of smart contract vulnerabilities highlights the need for more rigorous auditing processes. This includes not only multiple independent audits but also greater adoption of formal verification methods, which mathematically prove the correctness of smart contract code. Incentivizing bug bounty programs also plays a crucial role in identifying flaws before exploitation.
The industry is moving towards a standard where critical smart contracts undergo several rounds of audits by different firms, along with extensive testing frameworks. This multi-pronged approach aims to catch even the most elusive bugs that attackers often exploit.
Improving operational security for crypto entities
Many 2025 incidents stemmed from weak operational security practices, such as compromised private keys, insufficient access controls, and inadequate employee training. Crypto exchanges, DeFi protocols, and other entities must implement stringent operational security protocols, including multi-signature requirements, hardware security modules (HSMs), and regular security awareness training for staff.
- Mandatory multi-factor authentication for all critical systems and accounts.
- Regular penetration testing and red team exercises for crypto platforms.
- Implementation of robust incident response plans and disaster recovery protocols.
These measures are fundamental in creating a more secure operational environment, significantly reducing the attack surface for opportunistic and sophisticated threat actors.
International collaboration and policy alignment
Crypto hacks are inherently borderless, making international cooperation indispensable for effective prevention, investigation, and prosecution. The lessons from 2025 underscore the need for global policy alignment and enhanced collaboration among nations.
Cross-border intelligence sharing
Sharing threat intelligence across international borders is vital for tracking sophisticated criminal organizations that operate globally. This involves establishing secure channels for real-time information exchange between law enforcement agencies, cybersecurity firms, and regulatory bodies worldwide. Such collaboration can lead to faster identification and apprehension of perpetrators.
The US government is actively working with allies to develop standardized protocols for sharing data related to crypto crimes, facilitating more coordinated international responses. This includes joint task forces and multilateral agreements aimed at combating cybercrime effectively.
Harmonizing legal and regulatory approaches
Disparate legal and regulatory frameworks across different jurisdictions can create loopholes that cybercriminals exploit. Harmonizing these approaches, particularly concerning digital asset definitions, anti-money laundering (AML) regulations, and extradition treaties, can create a more unified front against crypto-related crime. This ensures that criminals cannot simply move their operations to less regulated environments.
The goal is to create a global ecosystem where bad actors have fewer places to hide, making it harder for them to profit from their illicit activities. International policy alignment is a long-term endeavor but one that is critical for the future of digital security.
| Key Point | Brief Description |
|---|---|
| Evolving Threats | 2025 saw increased sophistication in crypto hacks, targeting smart contracts, cross-chain bridges, and supply chains. |
| Forensic Methods | Advanced on-chain tracing and off-chain intelligence gathering were crucial for identifying perpetrators and understanding attack flows. |
| Proactive Security | Emphasis on rigorous smart contract auditing, formal verification, and improved operational security for crypto entities in 2026. |
| Policy & Collaboration | Need for enhanced regulatory frameworks, international intelligence sharing, and harmonized legal approaches to combat global cybercrime. |
Frequently asked questions about crypto security
In 2025, attackers primarily exploited vulnerabilities in smart contracts, conducted flash loan attacks, targeted cross-chain bridges, and compromised supply chains of crypto projects. Social engineering also remained a significant threat, often leading to private key compromises and unauthorized access to digital assets.
Forensic analysis helps by meticulously tracing stolen funds across various blockchain networks and mixer services. By analyzing transaction patterns and leveraging off-chain intelligence, investigators can identify the destinations of illicit funds, potentially leading to their freezing and eventual recovery through legal channels and international cooperation.
Smart contract audits are crucial for identifying and rectifying vulnerabilities before deployment. Rigorous audits, ideally by multiple independent firms, combined with formal verification methods, can significantly reduce the risk of exploits. They ensure the code behaves as intended, preventing logical flaws that attackers commonly target.
Strengthening US digital security involves multiple strategies: implementing more robust regulatory frameworks, investing in advanced forensic capabilities and threat intelligence, promoting proactive security measures like formal verification, and fostering international collaboration to combat cross-border cybercrime effectively. Education and awareness are also key for users.
International collaboration is paramount because crypto hacks are global in nature. Sharing threat intelligence, harmonizing legal and regulatory frameworks, and establishing joint task forces enable faster detection, more effective investigation, and successful prosecution of cybercriminals operating across borders. This creates a unified front against illicit activities.
Conclusion
The forensic analysis of crypto hacks in 2025 provides a stark but invaluable blueprint for bolstering US digital security in 2026. The shift towards more sophisticated attack vectors targeting complex DeFi protocols and cross-chain bridges necessitates a proactive and multi-faceted defensive strategy. By embracing enhanced regulatory frameworks, investing in cutting-edge forensic capabilities, prioritizing rigorous smart contract auditing, and fostering robust international collaboration, the United States can significantly fortify its defenses against the ever-evolving landscape of crypto cybercrime. The lessons learned are not merely reactive; they are foundational for building a resilient and secure digital future.





