Zero-Trust Web3 Architectures: 2026 US Security Standards

Zero-Trust Architectures are fundamentally transforming Web3 security in the US, establishing a robust framework that mandates continuous verification for all users and devices, thereby meeting and exceeding the stringent 2026 security standards.
As the digital landscape evolves at an unprecedented pace, particularly within the decentralized realm of Web3, the need for robust security measures becomes paramount. In the United States, the implementation of Zero-Trust Architectures for Web3: Implementing 2026 Security Standards in the US is emerging as a critical framework to safeguard digital assets and user privacy. This shift isn’t merely an upgrade; it’s a foundational reimagining of how trust and access are managed in a world where traditional perimeter-based security is no longer sufficient.
Understanding the imperative for zero-trust in Web3
The decentralized nature of Web3, while offering immense opportunities, also presents unique security challenges. Traditional security models, which assume trust within a network perimeter, are fundamentally incompatible with Web3’s distributed and open environment. This incompatibility necessitates a paradigm shift towards a ‘never trust, always verify’ approach, which is the core tenet of Zero-Trust Architectures. In the US, regulators and industry leaders are increasingly recognizing that adopting these architectures is not just best practice, but a prerequisite for future digital resilience.
The vulnerabilities inherent in Web3, such as smart contract exploits, phishing attacks targeting decentralized applications (dApps), and compromised private keys, underscore the urgency. A single point of failure in a centralized system can be devastating, but in Web3, the attack surface is often broader and more complex due to interconnected protocols and user interactions. Zero-trust aims to mitigate these risks by treating every access attempt, regardless of origin, as potentially malicious.
The evolving threat landscape in decentralized finance
Decentralized finance (DeFi) has been a hotbed of innovation, but also a prime target for cybercriminals. The considerable value locked in DeFi protocols makes them attractive targets, leading to significant losses from hacks and exploits. The continuous evolution of attack vectors demands a security framework that is adaptive and resilient.
- Sophisticated Smart Contract Exploits: Attackers find subtle vulnerabilities in smart contract code, leading to asset drains.
- Supply Chain Attacks: Compromising a component in the development or deployment process of Web3 applications.
- Identity-based Attacks: Targeting user wallets and private keys through social engineering or malware.
- Protocol-level Vulnerabilities: Exploiting weaknesses in the underlying blockchain or consensus mechanisms.
By implementing zero-trust principles, organizations can establish granular access controls and continuous authentication, significantly reducing the likelihood and impact of such attacks. This proactive stance is crucial for building trust and ensuring the long-term viability of Web3 innovations within the US market.
The push for Zero-Trust Architectures in Web3 is driven by the recognition that traditional security models are ill-equipped to handle the unique challenges of decentralized systems. The inherent vulnerabilities in Web3, from smart contract exploits to sophisticated identity-based attacks, demand a ‘never trust, always verify’ approach to protect digital assets and user privacy effectively. This strategic shift is vital for fostering a secure and resilient Web3 ecosystem in the US.
Core principles of zero-trust applied to Web3
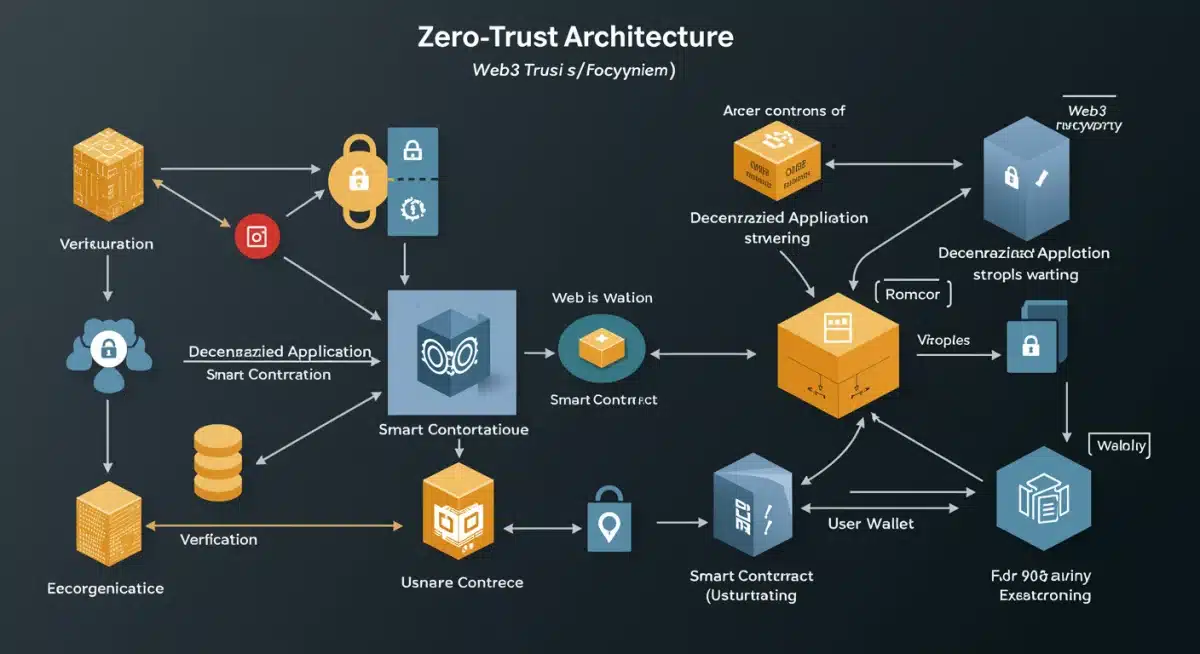
Applying the core principles of zero-trust to the Web3 environment involves a fundamental rethinking of how interactions and transactions are secured. At its heart, zero-trust mandates that no user, device, or application is inherently trusted, even if it’s within the network’s perceived boundaries. Every access request must be authenticated, authorized, and continuously validated. This approach translates into a series of interconnected security layers that work in concert to protect decentralized systems.
The implementation begins with strong identity verification, moving beyond simple password authentication to multi-factor authentication (MFA) and decentralized identity (DID) solutions. Access to dApps, smart contracts, and blockchain resources is then granted based on the principle of least privilege, ensuring users only have the necessary permissions for their immediate task. Continuous monitoring and threat detection are also paramount, enabling real-time responses to anomalies and potential breaches.
Key pillars for zero-trust implementation
Successfully integrating zero-trust into Web3 requires a focus on several critical areas:
- Decentralized Identity (DID): Leveraging blockchain-based identities for verifiable credentials and self-sovereign identity management.
- Micro-segmentation: Dividing network access into smaller, isolated segments, limiting lateral movement for attackers.
- Multi-Factor Authentication (MFA) and Adaptive Access: Requiring multiple forms of verification and adjusting access policies based on real-time risk assessments.
- Continuous Monitoring and Analytics: Employing AI/ML-driven tools to detect unusual patterns and potential threats across the Web3 stack.
These pillars collectively form a robust defense strategy, moving away from perimeter-centric security towards a more dynamic and context-aware model. For Web3, this means securing not just the network, but every individual interaction with a smart contract or dApp. This rigorous approach ensures that even if one component is compromised, the blast radius is minimized, protecting the broader ecosystem.
The application of zero-trust principles in Web3 fundamentally changes how security is managed, moving from implicit trust to explicit, continuous verification. This involves strong identity verification, least privilege access, and constant monitoring across all interactions. By focusing on decentralized identity, micro-segmentation, advanced authentication, and continuous analytics, Web3 can build a more secure and resilient foundation against evolving threats.
2026 security standards in the US: what to expect
The year 2026 marks a significant milestone in digital security within the United States, particularly concerning Web3 technologies. Federal agencies, industry bodies, and cybersecurity organizations are converging on a set of stringent security standards that will heavily influence the development and deployment of decentralized applications and blockchain infrastructure. These standards are largely built upon the foundation of Zero-Trust Architectures, reflecting a national commitment to enhanced digital resilience.
Expect a stronger emphasis on regulatory compliance, with frameworks like NIST (National Institute of Standards and Technology) playing a pivotal role in shaping guidelines for zero-trust adoption in Web3. This will likely include mandatory requirements for data encryption, secure coding practices for smart contracts, and verifiable proofs of identity for participants in decentralized networks. The goal is to create a more secure and trustworthy digital environment, protecting both consumers and critical infrastructure from sophisticated cyber threats.
Key areas of focus for 2026 standards
Several critical areas are expected to be prioritized in the upcoming 2026 security standards:
- Mandatory Zero-Trust Implementation: Widespread adoption of zero-trust principles across all government-related Web3 projects and incentivized for private sector.
- Enhanced Smart Contract Audits: Stricter requirements for independent security audits of smart contracts before deployment, utilizing advanced static and dynamic analysis tools.
- Interoperable Decentralized Identity: Promotion of standardized, interoperable decentralized identity solutions to streamline secure access and verification across Web3 platforms.
- Supply Chain Security for Web3: Comprehensive measures to secure the entire software supply chain for decentralized applications, from development to deployment.
These anticipated standards represent a proactive step by the US to cement its leadership in digital security, fostering an environment where Web3 innovations can thrive securely. Companies operating within the Web3 space in the US will need to align their security strategies with these evolving regulations to ensure compliance and maintain competitive advantage. The future of Web3 security in the US is intrinsically linked to the successful integration of these advanced, zero-trust-centric standards.
The 2026 security standards in the US will significantly impact Web3, prioritizing Zero-Trust Architectures, robust data encryption, and verifiable identity. These regulations, influenced by NIST, aim to enhance digital resilience and protect against cyber threats. Key focus areas include mandatory zero-trust adoption, stringent smart contract audits, interoperable decentralized identity, and comprehensive supply chain security for Web3 applications.
Implementing zero-trust: challenges and solutions in Web3
While the benefits of Zero-Trust Architectures for Web3 are clear, their implementation presents a unique set of challenges. The decentralized and often pseudonymous nature of blockchain networks can complicate traditional identity management, a cornerstone of zero-trust. Additionally, the immutability of smart contracts means that once deployed, vulnerabilities are difficult and sometimes impossible to patch without significant effort or a complete redeployment, which can be costly and disruptive.
Another hurdle lies in the complexity of integrating zero-trust principles across diverse Web3 ecosystems, which often consist of multiple blockchains, layer-2 solutions, and various dApps. Achieving consistent policy enforcement and granular access control in such a fragmented environment requires innovative approaches. However, solutions are emerging, driven by advancements in cryptographic techniques, decentralized identity protocols, and AI-powered security analytics.
Overcoming implementation hurdles
Addressing these challenges requires a multifaceted strategy:
- Decentralized Identity (DID) Frameworks: Utilizing DIDs to provide verifiable and self-sovereign identity management, allowing users to control their data while enabling robust authentication.
- Automated Smart Contract Audits and Formal Verification: Employing AI-driven tools and mathematical proofs to identify and eliminate vulnerabilities in smart contracts pre-deployment.
- Cross-Chain Interoperability with Security Layers: Developing secure bridges and protocols that incorporate zero-trust checks for transactions and data transfers between different blockchains.
- Behavioral Analytics and Anomaly Detection: Implementing advanced analytics to continuously monitor user and application behavior on Web3 networks, flagging suspicious activities in real-time.
These solutions are crucial for bridging the gap between theoretical zero-trust principles and practical Web3 deployment. By focusing on these areas, developers and enterprises can build more secure decentralized applications that meet the evolving security demands, including the 2026 US standards. The journey to a fully zero-trust Web3 environment is ongoing, but with continuous innovation, these challenges are steadily being overcome.
Implementing Zero-Trust Architectures in Web3 faces challenges like decentralized identity management and smart contract immutability. Solutions involve leveraging Decentralized Identity (DID) frameworks, automated smart contract audits, secure cross-chain interoperability, and behavioral analytics. These strategies are vital for building secure dApps that meet 2026 US security standards and overcome the complexities of a fragmented Web3 ecosystem.
The role of decentralized identity in zero-trust Web3
Decentralized Identity (DID) is a cornerstone of effective Zero-Trust Architectures within the Web3 paradigm. Traditional identity systems are centralized, making them single points of failure vulnerable to breaches and censorship. In Web3, where trust is distributed and user control is paramount, DIDs offer a revolutionary alternative. They allow individuals and entities to own and manage their digital identities without reliance on a central authority, issuing verifiable credentials that can be cryptographically proven.
For zero-trust, DIDs enable a robust and granular approach to authentication and authorization. Instead of relying on a third-party intermediary, users can present verifiable proofs of their attributes directly to a dApp or service, which can then verify these claims on the blockchain. This empowers users with greater privacy and control over their personal data, while simultaneously providing Web3 services with a trustworthy mechanism to verify identities and enforce access policies based on the ‘never trust, always verify’ principle.
How DIDs enhance zero-trust for Web3
DIDs bring several significant advantages to the zero-trust model in Web3:
- Self-Sovereign Identity: Users control their identity data, granting selective access to dApps as needed, aligning with least privilege principles.
- Tamper-Proof Verification: Verifiable credentials, issued and attested on a blockchain, ensure that identity claims are immutable and trustworthy.
- Reduced Attack Surface: Eliminates centralized identity repositories, reducing the risk of large-scale data breaches.
- Enhanced Privacy: Users can prove attributes (e.g., age over 21) without revealing their full identity, crucial for privacy-preserving zero-trust.
The synergy between DIDs and zero-trust is critical for meeting 2026 US security standards. By providing a secure, private, and verifiable means of identification, DIDs enable the granular access controls and continuous authentication necessary for a truly zero-trust Web3 environment. This integration is not just about security; it’s about building a more equitable and privacy-preserving digital future.
Decentralized Identity (DID) is crucial for Zero-Trust Architectures in Web3, providing a secure, user-controlled identity system. DIDs enable robust authentication and authorization by allowing verifiable, blockchain-attested credentials, eliminating centralized points of failure. This enhances self-sovereignty, ensures tamper-proof verification, reduces attack surfaces, and improves privacy, all vital for meeting 2026 US security standards and fostering a secure Web3 ecosystem.
Integrating zero-trust with smart contract security
Smart contracts are the backbone of Web3, automating agreements and transactions without intermediaries. However, their immutability, while a strength, also makes them a significant security vulnerability if not properly secured. Integrating Zero-Trust Architectures with smart contract security is therefore paramount, ensuring that these self-executing agreements are not only functional but also resilient against exploits. A zero-trust approach mandates that every interaction with a smart contract, whether by a user or another contract, is treated with suspicion and rigorously verified.
This integration involves a multi-layered strategy, starting from the design phase of the smart contract itself. Secure coding practices, formal verification methods, and extensive auditing become non-negotiable. Furthermore, runtime monitoring and access controls, enforced through zero-trust principles, ensure that even after deployment, smart contract interactions are continuously validated against predefined policies and behavioral baselines. This proactive and reactive security posture is essential for preventing vulnerabilities from being exploited.
Strategies for secure smart contract interaction
To effectively integrate zero-trust with smart contract security, several strategies are vital:
- Pre-deployment Audits and Formal Verification: Thorough, independent security audits and mathematical proofs to verify contract logic and identify vulnerabilities before deployment.
- Role-Based Access Control (RBAC) within Contracts: Implementing granular permissions within smart contracts, allowing only authorized addresses or DIDs to execute specific functions.
- Continuous Runtime Monitoring: Utilizing AI-powered tools to observe smart contract behavior for anomalies or deviations from expected patterns.
- Emergency Pause/Upgrade Mechanisms: Incorporating failsafe mechanisms in contracts to pause operations or allow for secure upgrades in case of critical vulnerabilities.
By embedding zero-trust principles directly into the lifecycle of smart contracts, from design to execution, Web3 developers can significantly enhance their security posture. This approach minimizes the risk of unauthorized access, malicious interactions, and costly exploits, aligning with the stringent security expectations outlined in the 2026 US standards. A secure Web3 future depends heavily on this symbiotic relationship between zero-trust and smart contract integrity.
Integrating Zero-Trust Architectures with smart contract security is crucial for Web3. This involves rigorous verification of all smart contract interactions, from design to execution. Strategies include pre-deployment audits, formal verification, role-based access control within contracts, continuous runtime monitoring, and emergency mechanisms. This multi-layered approach is essential to prevent exploits and meet the demanding 2026 US security standards.
Future outlook: zero-trust and Web3’s evolution in the US
The trajectory of Web3 innovation in the US is inextricably linked to the continued evolution and widespread adoption of Zero-Trust Architectures. As we look towards 2026 and beyond, zero-trust will not merely be a security framework but a fundamental operating principle embedded in the very fabric of decentralized applications, protocols, and digital identities. This integration will foster a more resilient, trustworthy, and user-centric Web3 ecosystem, driving further adoption and economic growth.
The US government’s increasing focus on cybersecurity, coupled with industry-led initiatives, will accelerate the development of standardized zero-trust solutions tailored for Web3’s unique challenges. Expect greater collaboration between public and private sectors to establish best practices, develop advanced security tools, and train a new generation of cybersecurity professionals skilled in decentralized security. This concerted effort will ensure that the US remains at the forefront of Web3 innovation, while prioritizing the safety and privacy of its citizens.
Emerging trends and technologies
- AI-Powered Security Orchestration: Leveraging AI for automated threat detection, incident response, and adaptive policy enforcement in zero-trust Web3 environments.
- Quantum-Resistant Cryptography: Research and implementation of cryptographic methods that can withstand future quantum computing attacks, securing zero-trust foundations.
- Privacy-Enhancing Technologies (PETs): Integration of PETs like zero-knowledge proofs (ZKPs) to enable verifiable, privacy-preserving authentication and authorization within zero-trust models.
- Decentralized Security-as-a-Service (DSaaS): The emergence of decentralized platforms offering zero-trust security solutions, making advanced protection accessible to all Web3 projects.
The future of Web3 in the US is bright, propelled by a security paradigm that emphasizes continuous verification and minimal trust. By embracing Zero-Trust Architectures, the US is not only meeting the 2026 security standards but also laying the groundwork for a more secure, robust, and innovative decentralized internet. This proactive stance will undoubtedly inspire global adoption and set new benchmarks for digital security.
The future of Web3 in the US is deeply intertwined with Zero-Trust Architectures, making them fundamental operating principles for decentralized applications. This integration, driven by government and industry collaboration, will enhance Web3’s resilience and trustworthiness. Key trends include AI-powered security, quantum-resistant cryptography, privacy-enhancing technologies, and Decentralized Security-as-a-Service, all contributing to a more secure and innovative decentralized internet.
| Key Aspect | Brief Description |
|---|---|
| Zero-Trust Principle | ‘Never trust, always verify’ for all users, devices, and applications within Web3. |
| 2026 US Standards | Mandatory adoption of zero-trust, enhanced smart contract audits, and secure supply chains. |
| Decentralized Identity (DID) | Crucial for verifiable, self-sovereign identity management in Web3 zero-trust models. |
| Smart Contract Security | Integration of zero-trust with pre-deployment audits and continuous runtime monitoring. |
Frequently asked questions about zero-trust Web3 security
Zero-Trust Architecture in Web3 is a security model that assumes no user or device is trustworthy by default, regardless of its location. It requires continuous verification for every access attempt to decentralized applications, smart contracts, and blockchain resources, significantly enhancing security in distributed environments.
The 2026 US security standards prioritize zero-trust for Web3 due to the unique vulnerabilities of decentralized systems, such as smart contract exploits and identity-based attacks. These standards aim to establish a robust, adaptive framework that protects digital assets and ensures the integrity of the evolving Web3 ecosystem nationwide.
Decentralized Identity (DID) is crucial for zero-trust in Web3 by enabling self-sovereign identity management. Users control their verifiable credentials, allowing for granular, privacy-preserving authentication and authorization without central authorities. This aligns perfectly with the ‘never trust, always verify’ principle, strengthening overall security.
Key challenges include managing identities in pseudonymous blockchain environments, securing immutable smart contracts, and achieving consistent policy enforcement across diverse Web3 ecosystems. Overcoming these requires innovative solutions like advanced cryptographic techniques, AI-driven analytics, and secure cross-chain interoperability protocols.
Future trends include AI-powered security orchestration for automated threat detection, quantum-resistant cryptography to protect against future attacks, and privacy-enhancing technologies like zero-knowledge proofs for secure authentication. These innovations will further strengthen zero-trust foundations, ensuring Web3’s secure evolution in the US.
Conclusion
The journey towards fully securing the decentralized frontier of Web3 in the United States is being decisively shaped by the adoption of Zero-Trust Architectures. As 2026 approaches, these standards are not just a regulatory mandate but a fundamental shift in how we perceive and manage digital trust. By embracing a ‘never trust, always verify’ philosophy, coupled with advancements in decentralized identity, smart contract security, and continuous monitoring, the US is poised to create a robust and resilient Web3 ecosystem. This proactive approach will undoubtedly foster innovation, protect users, and solidify the nation’s leadership in the global digital landscape, ensuring a safer and more trustworthy future for all participants.